I draw the line at when a third party internet-connected service is doing validation of ID. Let’s be honest though, I strongly believe such a thing isn’t possible on a FOSS operating system environment unless they could control what was bootable on the device at a firmware level, enforce signatures to ensure that you couldn’t boot something unrestricted, remove the ability to be root, and block LD_PRELOAD so signals couldn’t be faked. There’s probably more ways to circumvent that.
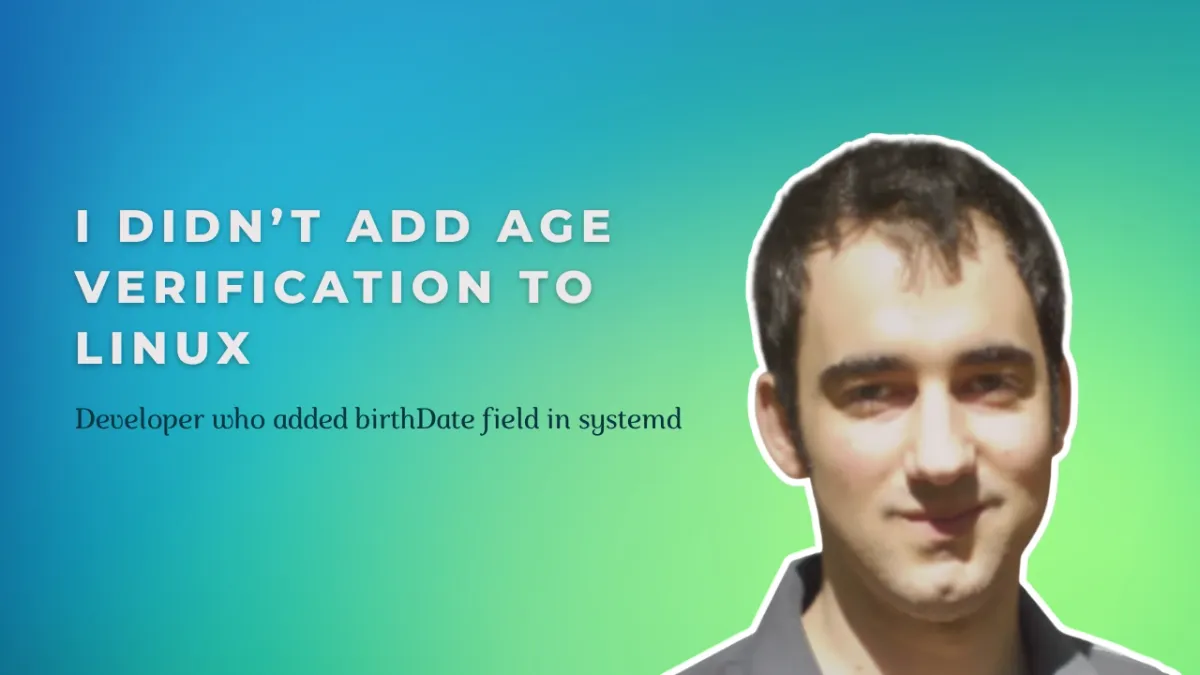
What I’m trying to say is real ID verification on Linux would be awfully hard to implement, and I guarantee you, nobody would put up with it. They’d fork to a version that doesn’t have it immediately as a protest. Right now, we’re considering implementing something akin to the date pickers that were ubiquitous when signing up for internet services in the early 2000s where it’s just an honor system.


I grew up in that situation so believe me, the abusive parents are going to find a way to be abusive regardless.
Ignoring how impractical it would be to accurately enforce, said parent would simply… not give them computer access to the outside world at all, or just change a password. In my case, they tried to limit access using router mac address rules 🤣